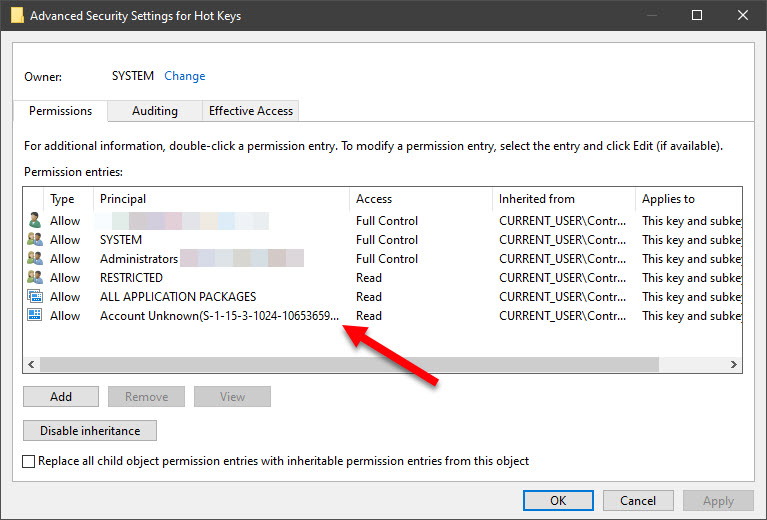
I was poking around my Windows 10 registry and stumbled across an “account unknown” SID – which immediately triggered my “hack alert” (not to mention my OCD)…
I traced this inherited permission up to registry root – which got me really worried…
I was about to just “try and clean it up” (e.g. search the entire registry for the same SID and delete it if no such value, i.e. reference, was found), but decided to quickly search the ‘net while waiting for regedit to complete the full tree search when I stumbled upon this.
TLDR: Don’t blindly delete any unknown SIDs…
<RANT> Trust Microsoft to do something stupid like this, all in the name of attempting to “hide” or obfuscate their spying (in the case of this specific SID “S-1-15-3-1024-1065365936-1281604716-3511738428-1654721687-432734479-3232135806-4053264122-3456934681” in question); I mean, why would Edge, one piece of software requiring outbound network connectivity, need to have read permissions of the entire freakin’ registry?!?). This looks like one massive data leak/breach (via an Edge exploit) waiting to happen.</RANT>